The best solutions
to protect your company information. Manage information security and mobile devices from the cloud, no matter where you are.
Adaptive Defense is a revolutionary new security model that ensures complete protection for devices, computers, and servers by classifying 100% of the processes running on the computer and blocking executable files.
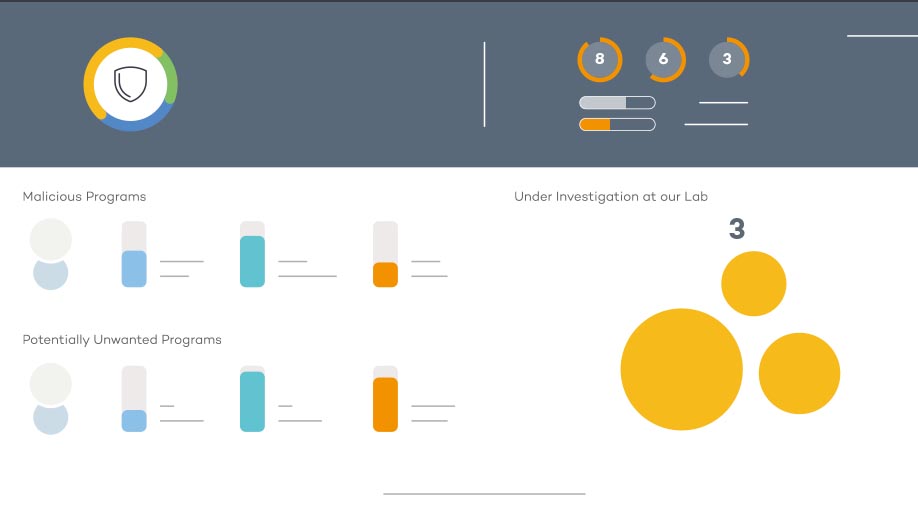
is the first cyber security service of its kind that combines the most effective features of traditional antivirus solutions and advanced protection with the ability to classify all executable processes.
WHY DO YOU NEED ADAPTIVE DEFENSE IF YOU ALREADY HAVE AN ANTIVIRUS IN YOUR COMPANY?
The volume of malicious code is growing at a very fast pace on a daily basis (over 200,000 new threats every day) and is becoming more difficult to detect by traditional antivirus solutions. The reality of that, combined with increasingly complex corporate networks and the challenges facing IT departments, allows hackers to break into corporate networks, making a huge amount of threats to go unnoticed for a long time. Traditional antivirus solutions are not enough because they can only process so many definitions and cannot integrate protection at the level of target attacks and executable files (crypto viruses). They only use strategies based on antivirus definitions and heuristic algorithms.
THE SOLUTION: The advanced reporting tool of Panda Security
It automates the storage and links between information received from the Adaptive Defense 360, emphasizing on processes running on all devices. Through the information received, the tool automatically investigates and provides tools to specify attacks, attempted attacks, non-standard program behavior, regardless of origin, and detects internal abuses in the corporate network.
The advanced reporting tool provides the collected information + tips how to manage corporate IT security. They can be used to create an action plan focusing on:
Find relevant information:
Control access to important business information:
Save money:
Real-time alarms:
Create alarms for various events
